Build a Serverless Architecture to Analyze Amazon CloudFront Access Logs Using AWS Lambda, Amazon Athena, and Amazon Kinesis Analytics | AWS Big Data Blog

Enable private access to Amazon Redshift from your client applications in another VPC | AWS Big Data Blog

Perform multi-cloud analytics using Amazon QuickSight, Amazon Athena Federated Query, and Microsoft Azure Synapse - Blog - Amazon QuickSight Community

Build and load test a multi-tenant SaaS database proxy solution with Amazon RDS Proxy | AWS Database Blog

Simplify How You Manage Authorization in Your Applications with Amazon Verified Permissions – Now Generally Available | AWS News Blog
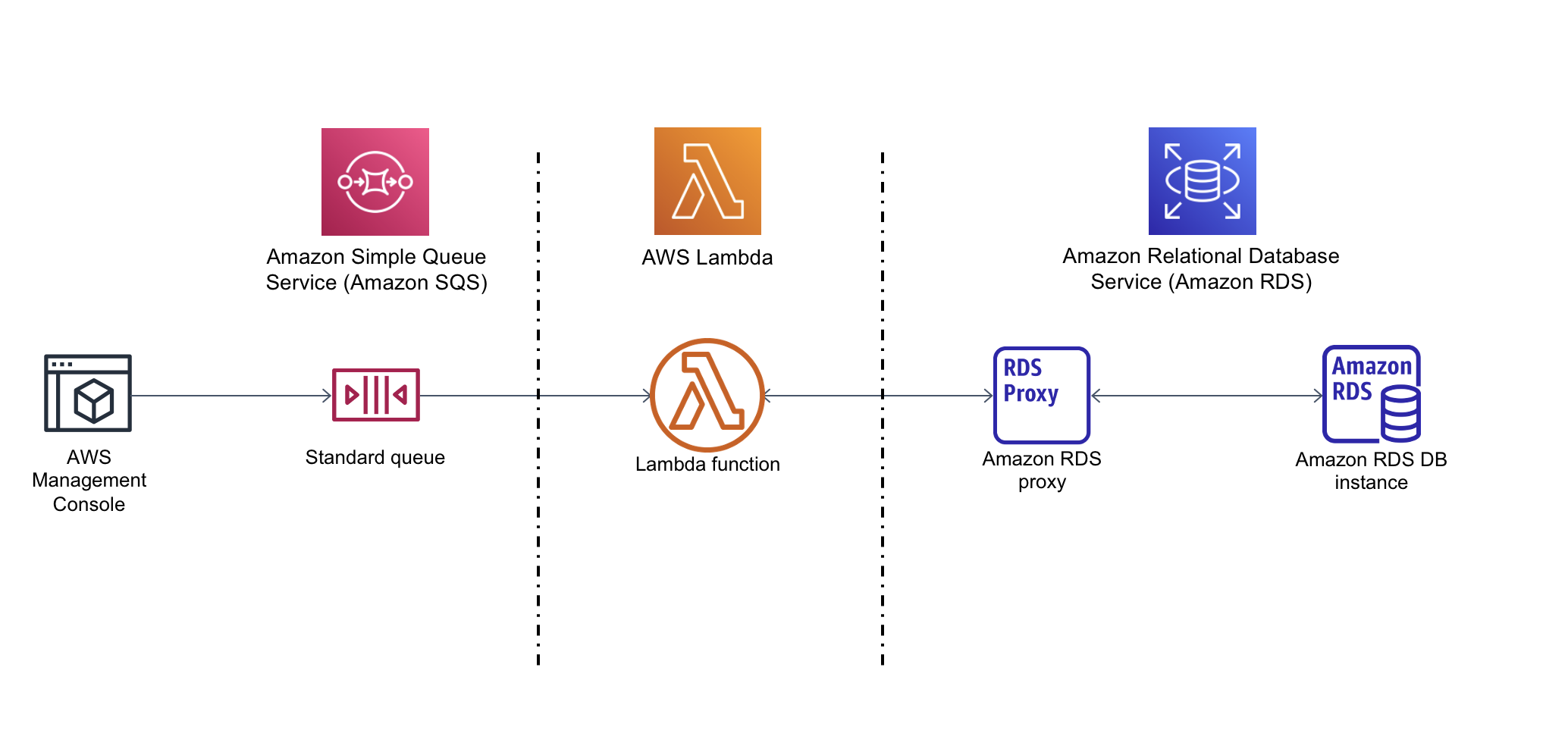
Tutorial: Using a Lambda function to access an Amazon RDS database - Amazon Relational Database Service

Create a multi-region Amazon Lex bot with Amazon Connect for high availability | AWS Machine Learning Blog

Build with Redis data structures for microservices using Amazon MemoryDB for Redis and Amazon ECS | AWS Database Blog

AWS Step Functions adds updates to 'choice' state, global access to context object, dynamic timeouts, result selection, and intrinsic functions to Amazon States Language | AWS News Blog
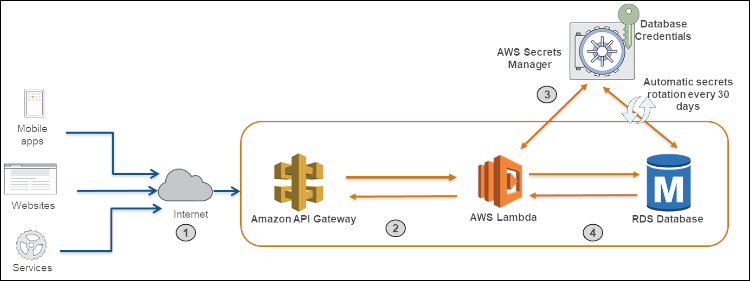
How to securely provide database credentials to Lambda functions by using AWS Secrets Manager | AWS Security Blog
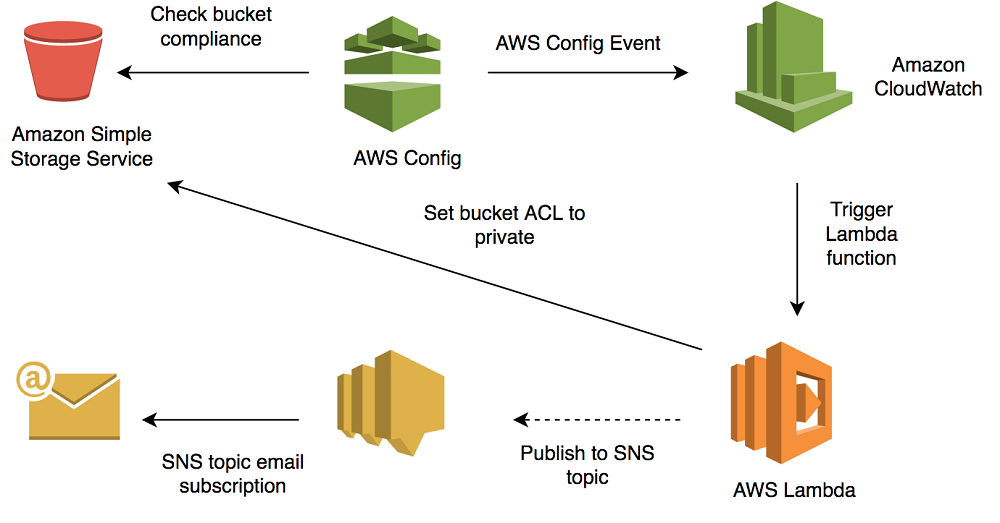
How to Use AWS Config to Monitor for and Respond to Amazon S3 Buckets Allowing Public Access | AWS Security Blog

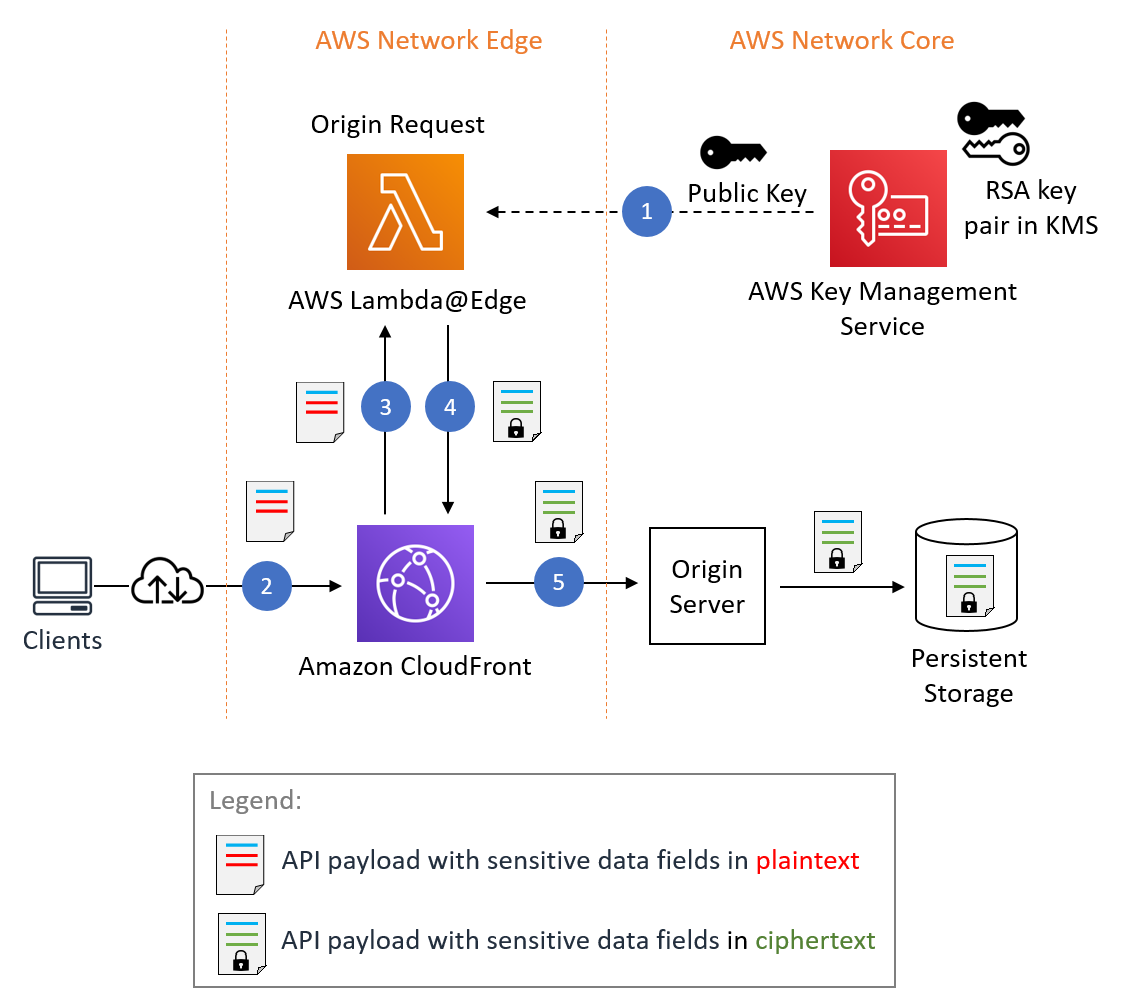
Authorization@Edge using cookies: Protect your Amazon CloudFront content from being downloaded by unauthenticated users | Networking & Content Delivery
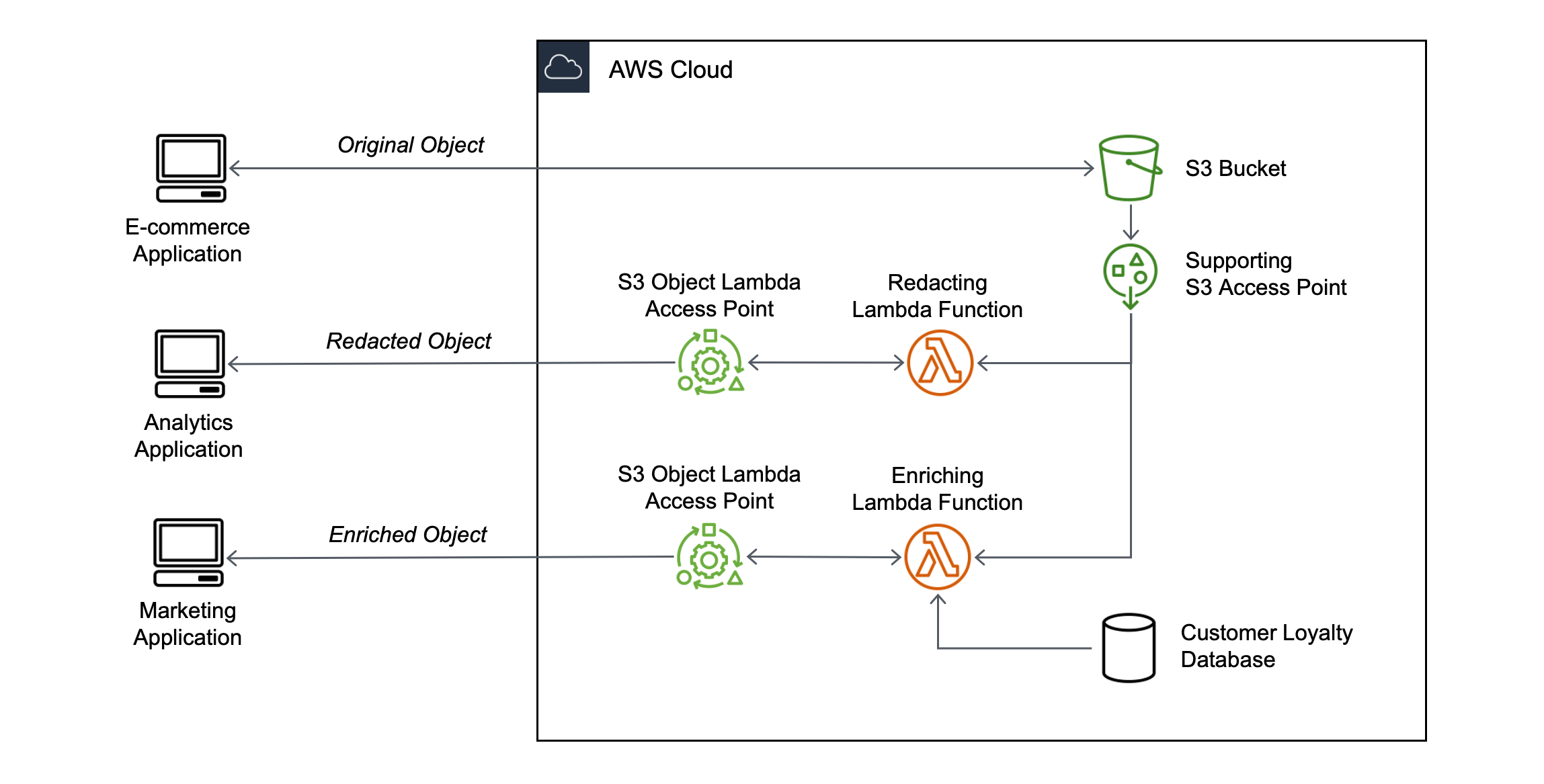
Introducing Amazon S3 Object Lambda – Use Your Code to Process Data as It Is Being Retrieved from S3 | AWS News Blog

Introducing CloudFront Functions – Run Your Code at the Edge with Low Latency at Any Scale | AWS News Blog